Here’s a clear and professional explanation of the three related concepts you asked about — all of which are critical parts of secure software development, especially in DevSecOps and open source software governance.
🧩 1. What is Software Composition Analysis (SCA)?
Software Composition Analysis (SCA) is the automated process of identifying, managing, and securing third-party and open source components used in your software project.
🔍 Purpose:
- Detect known vulnerabilities (CVEs) in dependencies
- Identify license types and violations
- Track open source usage (OSS inventory)
- Ensure security, legal, and compliance in your codebase
🧪 What It Does:
| Function | Description |
|---|---|
| 📦 Detect dependencies | Parses package.json, pom.xml, etc. |
| 🔐 Find vulnerabilities | Matches against CVE/NVD databases |
| ⚖️ Check licenses | Verifies if licenses (GPL, MIT, etc.) violate policy |
| 🧾 Inventory generation | Creates SBOM (Software Bill of Materials) |
| 🔄 Continuous monitoring | Alerts when new CVEs are published |
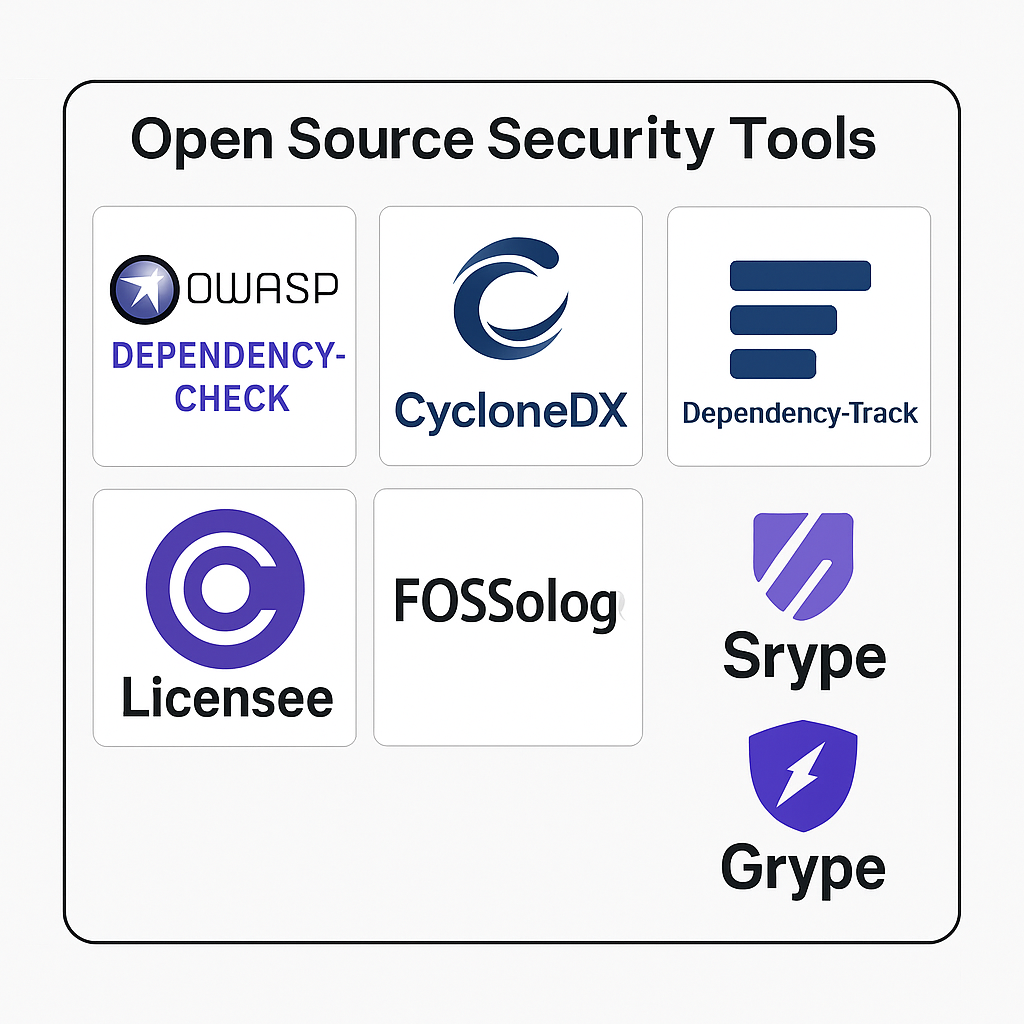
✅ Example Tools:
Snyk, OWASP Dependency-Check, Grype, Sonatype, Mend, Black Duck, FOSSA, Dependency-Track
🕵️♂️ 2. What is Dependency Check?
Dependency checking refers to analyzing software dependencies (external libraries, packages, frameworks) to:
- Detect known vulnerabilities (CVEs)
- Alert on outdated or deprecated versions
- Determine if any risky components are being used
📌 It’s part of SCA, but specifically focuses on identifying security flaws in imported packages.
🔐 How it works:
- Extracts dependency list (e.g., from
pom.xml,package-lock.json) - Queries vulnerability databases (like NVD)
- Flags packages with known CVEs
- Suggests safer versions (if supported)
✅ Example Tools:
- OWASP Dependency-Check (open source)
- Grype (by Anchore)
- Snyk (commercial + free tier)
- GitHub Dependabot
⚖️ 3. What is Open Source License Violation Check?
When you use open source software, you’re subject to its license terms (MIT, GPL, Apache, etc.).
Open Source License Checking ensures that:
- You don’t accidentally include a copyleft or viral license (like GPL) in proprietary software.
- Your use, distribution, or modification of code complies with the license.
- You meet legal obligations like attribution, redistribution rules, etc.
🚨 A “License Violation” Can Occur If You:
- Use GPL-licensed code in closed-source software
- Fail to provide attribution in MIT/BSD code
- Mix incompatible licenses in the same binary
✅ Tools That Detect License Violations:
- FOSSA (free/commercial)
- FOSSology (open source)
- Licensee (detects license from GitHub repos)
- Syft (shows license per package)
- Dependency-Track (shows license violations in SBOM)
🔄 Relationship Between the Three
| Area | SCA | Dependency Check | OSS License Check |
|---|---|---|---|
| Focus | Security + Legal + Inventory | Security (vulnerabilities) | Legal (licenses) |
| Input | Source code + package files | Dependencies (JAR, NPM, etc.) | LICENSE file, SPDX tags |
| Output | CVEs + License + SBOM | CVE alerts + upgrade paths | SPDX types, violation flags |
| Goal | Secure, compliant software | No vulnerable components | No legal risk from licenses |
📌 Real-World Example
Let’s say you’re building a JavaScript web app:
- SCA scans
package.jsonand tells you:- 1 high-risk CVE in
lodash - 3 dependencies under MIT, 1 under GPLv3 (incompatible with your business)
- 1 high-risk CVE in
- Dependency Check tells you:
lodash@4.17.15has CVE-2021-23337 → recommends upgrading to4.17.21
- License Checker tells you:
some-gpl-libviolates your license policy → you need to replace or isolate it
✅ Final Recommendation
To achieve full open-source security and compliance, combine:
| Task | Tool (Open Source Option) |
|---|---|
| CVE Detection | OWASP Dependency-Check / Grype |
| License Violation Check | FOSSology / Licensee / Syft |
| SBOM + Inventory | Syft / CycloneDX / Dependency-Track |
Here’s a detailed list of the Top 10 tools for Software Composition Analysis (SCA) — tools that analyze dependencies for:
- 🔐 Known vulnerabilities (CVEs)
- 🧾 Open source license compliance
- 📦 Outdated or risky libraries
- ⚖️ Policy violations and risk management
🔟 Top 10 SCA Tools (Vulnerability, License & OSS Risk)
| Tool Name | Best For | Key Features | License / CVEs | OSS License Check | Free Tier |
|---|---|---|---|---|---|
| Snyk | Modern apps (Node, Java, Python, etc.) | SCA + Fix PRs + Policy Gateways | ✅ | ✅ | ✅ |
| OWASP Dependency-Check | Open-source SCA scans | CVE scanning via NVD feeds | ✅ | Partial (SPDX tags) | ✅ |
| SonarQube | Enterprise-wide OSS risk mgmt | Compliance, security, reporting | ✅ | ✅ | ✅ |
| FOSSA | License compliance | Full SPDX license tree, CI/CD | ✅ | ✅ | ✅ (limited) |
| Black Duck (Synopsys) | Enterprise-grade SCA | Code matching, CVEs, license risks | ✅ | ✅ | ❌ |
| GitHub Dependabot | GitHub native alerts & PRs | Auto-update CVE-prone libs | ✅ | ❌ | ✅ |
| Sonatype Nexus Lifecycle | Java Maven Central guardian | DevSecOps, BOM tracking, CVE watch | ✅ | ✅ | ❌ |
| SourceClear (Veracode) | DevSecOps SCA w/ security focus | Java, Node.js, Ruby support | ✅ | ❌ | ❌ |
| CycloneDX + Dependency-Track | SBOM generation + CVE trace | SBOM analysis and license alerts | ✅ | ✅ | ✅ |
| Licensee (GitHub project) | OSS license checking | GitHub-compatible SPDX detection | ❌ | ✅ | ✅ |
🧪 Tool-by-Tool Breakdown
1. ✅ Snyk
- CLI + GitHub/GitLab integrations
- Real-time CVE scanning & fix suggestions
- License policies + developer PR fixes
- Supports: Java, Node, Python, Go, Docker
👉 snyk test + snyk monitor
2. ✅ OWASP Dependency-Check
- Free & open-source
- Maps dependencies to CVEs (NVD DB)
- CLI or Maven/Gradle plugin
- HTML, XML, JSON output
- Java, .NET, Node.js, Python support
👉 dependency-check --scan ./ --format HTML
3. 🏢 SonarQube Advanced Security (SCA)
Description: SonarQube Advanced Security brings developer-first SCA into the same workflow teams already use for code quality and SAST. It analyzes dependency manifests and lockfiles, continuously maps them to curated vulnerability and license data, and surfaces risks directly in PRs and CI/CD so developers can act without leaving their flow.
Key Features:
- Advanced SAST: Gain intelligence into how your code interacts with the broader software supply chain.
- Deep-tier taint detection: Uncover hidden vulnerabilities across complex data flows without adding overhead to your existing development workflow.
- Cross-boundary analysis: Trace interactions between your first-party code and open-source libraries to identify cascading security risks.
- SBOM and license governance: Automatically builds SBOMs, tracks license usage, and enforces license policies at the project and portfolio level to prevent problematic components from reaching production.
- Supply chain visibility: Highlights both direct and transitive dependencies, malicious or backdoored packages, and misconfigurations in dependency usage that can expose the broader software supply chain.
- Scales across ecosystems: Supports major languages and package managers (Maven/Gradle, npm/yarn, pip, NuGet, Go, PHP, Rust, Ruby, and more) with continuous expansion of coverage.
Pros:
- Single “pane of glass” for code quality, SAST, secrets, IaC, and SCA findings, making it easier for teams to understand and prioritize overall application risk.
- Low friction for developers because SCA is part of the same SonarQube analysis they already run on every change, with clear, actionable fixes instead of noisy CVE lists.
- Strong governance capabilities with SBOM export, policy-driven license enforcement, and portfolio-level reporting for security and compliance teams.
Cons:
- SCA is available as part of SonarQube Advanced Security (Enterprise Edition and above), so smaller teams or Community Edition users need to upgrade to access it.
- Dependency analysis can require additional configuration (build tool commands, lockfiles, network access) for highly customized or legacy build environments.
4. 📜 FOSSA
- Dev-friendly license compliance tool
- Full SPDX license support
- Detects copyleft, GPL, permissive licenses
- CLI + CI/CD integrations
5. 🏢 Black Duck (Synopsys)
- Legal compliance and full CVE map
- Detects unlicensed or unknown license code
- Ideal for regulated industries
- High precision in OSS detection
6. 🔒 GitHub Dependabot
- Auto-pulls CVE patch PRs to GitHub projects
- GitHub-native integration
- Simple license check in repo insights (basic)
- Good for fast-moving teams
7. 🛡️ Sonatype Nexus Lifecycle
- Deep OSS governance from Sonatype
- Maven Central-first intelligence
- Automatic quarantine of dangerous libs
- Excellent license policy enforcement
8. 🔍 Veracode SourceClear
- Focus on runtime + reachable vulnerabilities
- Lightweight SCA + SAST
- Used in highly secure CI/CD
9. 📦 CycloneDX + Dependency-Track
- SBOM generator (CycloneDX)
- Dependency-Track: CVE scanner for SBOMs
- Excellent for modern, multi-language apps
- Fully open source
10. ⚖️ Licensee
- GitHub project to detect repo licenses
- Supports SPDX license tags
- CLI or GitHub Action usage
licensee detect .
📊 Comparison Table: Summary View
| Tool | CVE Scan | License Scan | SBOM Support | GitHub CI/CD | Free Tier |
|---|---|---|---|---|---|
| Snyk | ✅ | ✅ | ✅ (partial) | ✅ | ✅ |
| OWASP Dep-Check | ✅ | Partial | ❌ | ✅ (custom) | ✅ |
| Mend (WhiteSource) | ✅ | ✅ | ✅ | ✅ | ❌ |
| FOSSA | ✅ | ✅ | ✅ | ✅ | ✅ |
| Black Duck | ✅ | ✅ | ✅ | ✅ | ❌ |
| Dependabot | ✅ | ❌ | ❌ | ✅ | ✅ |
| Sonatype Lifecycle | ✅ | ✅ | ✅ | ✅ | ❌ |
| SourceClear | ✅ | ❌ | ❌ | ✅ | ❌ |
| CycloneDX + DTrack | ✅ | ✅ | ✅ | ✅ | ✅ |
| Licensee | ❌ | ✅ | ❌ | ✅ | ✅ |
🧠 Recommendation by Use Case
| Use Case | Recommended Tool(s) |
|---|---|
| ✅ Free + Open Source CVE Check | OWASP Dependency-Check, DTrack |
| ✅ License Compliance for Legal | FOSSA, Black Duck, Sonatype |
| ✅ Auto PR Fixing | Snyk, Dependabot |
| ✅ SBOM Management | CycloneDX + Dependency-Track |
| ✅ All-in-One Enterprise SCA | Mend, Black Duck, Sonatype |
Based on the search results, here are excellent 100% open source and free tool combinations that cover License Scanning, CVE Detection, and OSS analysis:
Comprehensive All-in-One Solutions
OWASP Dependency-Check is your best single-tool option as it provides both CVE detection and partial license scanning capabilities9. It’s a powerful open-source tool that detects vulnerabilities in project dependencies across a wide range of package managers and programming languages, with access to an extensive vulnerability database and seamless CI/CD integration.
Trivy offers another comprehensive approach, detecting vulnerabilities (CVEs) in open source software while also including license scanning features that present risk assessments for projects in your dependency tree. It’s particularly strong for containerized workloads, checking container images for OS packages, CVEs, misconfigurations, leaked secrets, and software licensing issues.
Specialized Tool Combinations
For License Scanning Focus:
- FOSSology – A Linux Foundation project providing comprehensive open-source license compliance software with command line, database, and web UI capabilities for license, copyright, and export control scans
- ScanCode – Specializes in analyzing licensing, copyright, and vulnerability information, with detailed license compliance checks and support for multiple programming languages
- LicenseFinder – Detects licenses in project code, compares against user-defined whitelists, and provides actionable reports
For CVE Detection Excellence:
- OpenVAS – Comprehensive vulnerability scanner with over 50,000 known Network Vulnerability Tests, supporting authenticated and unauthenticated protocols
- Retire.js – Specialized for JavaScript codebases, scanning for known vulnerabilities in third-party libraries with continuous database updates from CVE sources
- OSV-Scanner – Excellent for library dependency vulnerability detection in web and app environments
Recommended Tool Combinations
Combination 1: Maximum Coverage
- Trivy (CVE detection + license scanning)
- FOSSology (comprehensive license compliance)
- OpenVAS (network vulnerability scanning)
Combination 2: Developer-Friendly
- OWASP Dependency-Check (CVE detection + basic license scanning)
- ScanCode (detailed license analysis)
- Retire.js (JavaScript-specific vulnerabilities)
Combination 3: CI/CD Optimized
- Trivy (container and dependency scanning)
- LicenseFinder (license management with whitelist/blacklist)
- OSV-Scanner (library dependency vulnerabilities)
Additional Specialized Tools
Syft works excellently for generating Software Bill of Materials (SBOM) with license information, particularly when paired with Grype for vulnerability scanning10. Ninka provides rapid license identification for quick scans11, while Code Janitor from The Linux Foundation helps evaluate source code for open source license compliance1.
All these tools are completely free, open source, and can be integrated into CI/CD pipelines. The combination you choose depends on your specific technology stack, with JavaScript projects benefiting from Retire.js, containerized applications from Trivy, and comprehensive enterprise needs from FOSSology paired with OpenVAS.
I’m a DevOps/SRE/DevSecOps/Cloud Expert passionate about sharing knowledge and experiences. I have worked at Cotocus. I share tech blog at DevOps School, travel stories at Holiday Landmark, stock market tips at Stocks Mantra, health and fitness guidance at My Medic Plus, product reviews at TrueReviewNow , and SEO strategies at Wizbrand.
Do you want to learn Quantum Computing?
Please find my social handles as below;
Rajesh Kumar Personal Website
Rajesh Kumar at YOUTUBE
Rajesh Kumar at INSTAGRAM
Rajesh Kumar at X
Rajesh Kumar at FACEBOOK
Rajesh Kumar at LINKEDIN
Rajesh Kumar at WIZBRAND
Find Trusted Cardiac Hospitals
Compare heart hospitals by city and services — all in one place.
Explore Hospitals