- System Hardening Overview
- Batille
- Securing X-Windows
- Securing Linux Daemons
- Security patches
- Security Benchmarks
System Hardening Overview
- Linux, like other operatingsystems, is not secure “out of the box”
- Security increases as newer versions and distros come out
- Users/administrators still need to take steps to “harden” systems
- Items typically requiring securing/hardening include:
- X-Windows
- System daemons
- Networking services
Bastille
- Scripts walk SA through several modules, automates changing a large number of configurable system items
- Has modules for checking and configuring Internet services, suid(set-user-ID) files, account and boot security, and TCP wrappers
- Bastille program is available from http://bastille-linux.sourceforge.net/
- Bastille currently supports most distros of Linux and Unix including:
- Red Hat, SuSe, Debian, Gentoo, Mandrake, and HP-UX
Securing X-Windows
- X-windows is Graphical Interface for Linux
- Comes with most distributions,but is ot part of them
- Used to access systems both locally and remotely
- X is a Protocol and set of utilities
- Client-server design
- Runs from the X server, and provides keyboard, mouse and video
- Not configured securely by default
- Signals can get intercepted btween x-server and client(either remote or local)
- Several ways of securing X
- xhost – controls authentication to x erver on a host basis
- X server maintains lists of allowed hosts
- xhost allows hosts to be added/deleted from list
- Vulnerabilities: Host spoofing, sessions are per host, not per user
- xauth – controls authentication through .Xauthority
- .Xauthority file contains authentication ‘cookie’ that client must send to server
- Best security mechanism is using X windows over ssh
- Authentication can be controlled and audited through user credentials
- communications traffic between x client and X erver is encrypted
Securing Linux Daemons
- Daemons are same as Windows services
- Programs that run in background to accomplish system tasks
- Often run with a set of credentials and privilege levels
- Securing Linux Daemons is to not install unnecessary ones!.
- Best way to secure daemons is to not install unnessary ones!
- Don’t use “Install Everything” option during installation
- Install services according to machine role
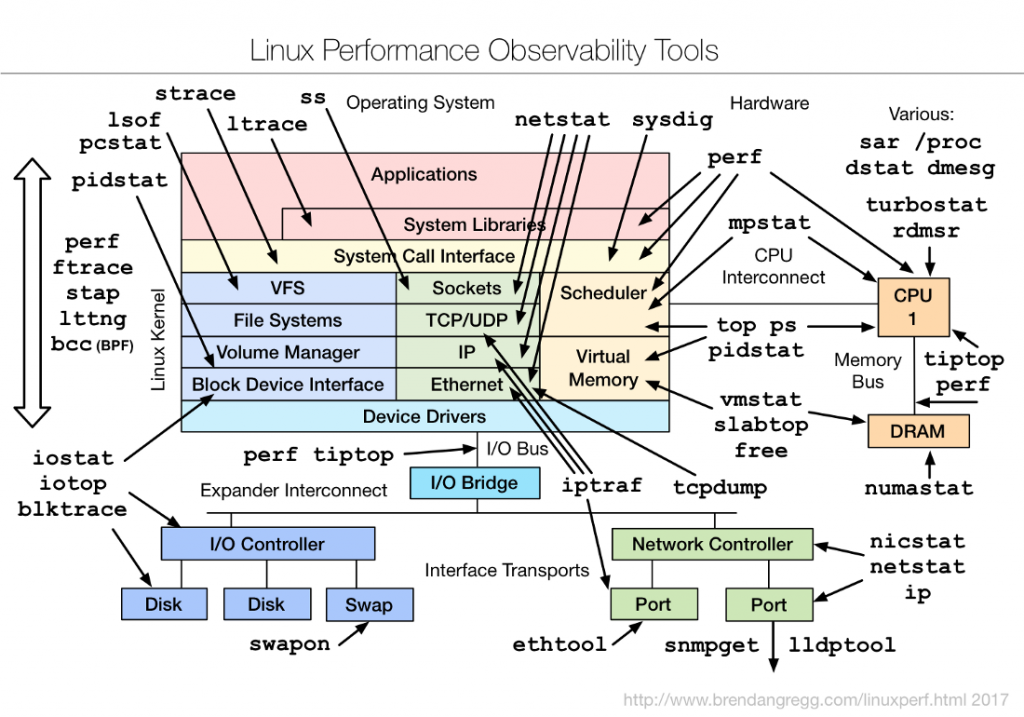
- Use ‘ps’ and ‘netstat’ commands to determine what services are running and network connections established by them
- Many Daemons turned on/off in /etc/inetd.conf – edit this file to selectively disable services that are not needed
- Recompiling kernel is another way to secure services
- Generate learner kernel with only daemons you need supported
- Eliminates risk of daemons being reconfigured or restarted
Security Patches
- Even after initial hardening, Linux can still be insecure
- New vulnerabilities discovered every day
- Security patches issued to counter threats and fix vulnerabilities
- Most current distros have automated patch utility
- Connects to trusted centralized site and downloads latest patches
- Usually provides patches for OS and popular software apps included in distro
- Third party apps frequently need patches from different vendors
- Usually manual download and installation process
- Download patches only from trusted sites
- Verify hashes provided with patches to ensure file integrity
- Many utilities to download and install security patches
- Up2date, YUM, and YaST are a few
- Get familiar with your distro’s update utilities
Security Benchmarks
- Several free and commercial tools exist to test/measure security on Linux
- Benchmarks available for almost all distros
- Usually automated tool that checks security of daemons, processes, accounts,permissions , etc.
- Nessus is free valnerability scanner provided with most distros
- Uses frequently updated database of vulnerabilities
- Can be used for single or multiple machines
- Uses client/server architecture
I’m a DevOps/SRE/DevSecOps/Cloud Expert passionate about sharing knowledge and experiences. I have worked at Cotocus. I share tech blog at DevOps School, travel stories at Holiday Landmark, stock market tips at Stocks Mantra, health and fitness guidance at My Medic Plus, product reviews at TrueReviewNow , and SEO strategies at Wizbrand.
Do you want to learn Quantum Computing?
Please find my social handles as below;
Rajesh Kumar Personal Website
Rajesh Kumar at YOUTUBE
Rajesh Kumar at INSTAGRAM
Rajesh Kumar at X
Rajesh Kumar at FACEBOOK
Rajesh Kumar at LINKEDIN
Rajesh Kumar at WIZBRAND
Find Trusted Cardiac Hospitals
Compare heart hospitals by city and services — all in one place.
Explore Hospitals