- System Auditing
- System Logging
- Network Intrusion Detection with Snort
- Host File Integrity with Tripwire
System Auditing
- Auditing can track system activities to warn sysadmin of suspicious activity
- Allows sysadmin to understand the types of access that took place
- Can identify a security breach, and aid in the research of the breach
- More than simply logging or system accounting but they are component parts of auditing
- Other parts are intrusion detection and file verification, resource access, and privilege use
- Successful & unuccessful events both important
- Also involves analysis of dts and correlation of related events
- Some systems(i.e RHEL3 and SuSE Enterprise Linux) have special auditing software included
- Other distros can use ‘snare’ or ‘auditd’ for auditing functions
- Ensure audit data files can only be read by security auditors group
- Ensure the auditing software can record the following for each audit event:
- Date and time of the event
- Userid that initiated the event
- Type of event
- Success or failure of the event
- Origin of the request(IP or MAC address, host name ,etc)
- Retain audit data for at least one year(minimum)
- Ensure audit fles are backed up at least weekly onto a different system tha the one being audited or backup media
System Logging
- System logging is used to track events and when they occurred
- Used to identify system performance trends, keep a historical record of activities, and provide accountability for actions
- Logging must be managed, not simply turned and forgotten
- System log files refer to logs of system activities,such as the /var/log/syslog file, the /var/messages file, and others
- System logging is done via the sylog facility(syslogd)
- syslogd reas and forwards system messages to the log files and/or users
- /etc/syslog.conf is used to configure syslogd
- syslog can log bto local host or to centralized logging server
- Advantage of log server is that it allows centralized logging management for monitoring of possible malicious activity on network
- Many utilities log to syslogd by default or can be configured to do so
- syslogd should be secured to prevent log compromise, destruction, or unauthorized access
- Ensure reliable time source isused throghout network for accurate logging
- System logging normally takes place over port 514; services to this port should be resticated to local hosts at the firewall or premise router
- syslogd should be configured to accept messages only from designated hosts
- Ensure logs are reviewed daily
- Some messages need to be reviewed immediately by responsible sysadmin
- Archive logs at least daily to ease space requirements and to reduce the time requirements and to resuce the time required or log searches and reviews
Intrusion Detection With Snort
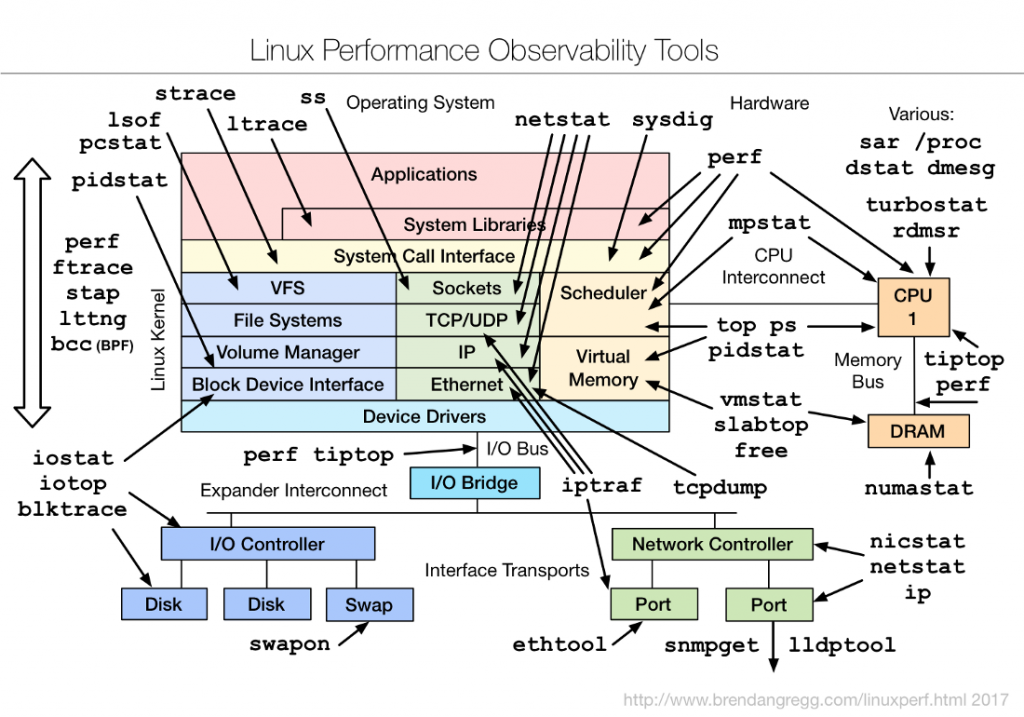
- Intrustion Detection Systems(IDS) monitor networks and hosts for unusual traffic patterns and behaviors to detect possible attacks
- IDS consists of sensors, collectors, databases, and analysis consoles
- Ability to detect attacks based upon knowns attack signatures or unusual activity (anomoly-based)
- IDS are host-based or Network-based
- Host-based(HIDS) detects attacks on a particular host
- Network-based(NIDS) detects unusual network traffic that may be an attack
- Snort is most popular open source IDS for Linux
- Signature-based NIDS that detects a wide variety of attacks
- Detected attacks include buffer overflows, Denial OF Service TCP/IP attacks Distributed DOS attacks, port scans and certain malware attacks
- Real-time Logging and alerting
- Highly configureable ruleset
- Ported to almst allLinux distros
- Configured through snot.conf file
- Uses the libpcap library as its packet detection engine
- Preprocesses packets before analysis to alert,filter,and modify potentailly harmfuyl traffic in advace
- Many types of preprocessors available.depending upon needed functionality
- After preprocessing, packets are delivered to the Rules Parsing and Detection Engine
- Reads configured rules and passes to detection engine for applcation to packets
- If packet matches a rule, Alerting an Logging engine logs details and fires and alert
- Logging can be done to centralized logging server
- Logs cn be text or binary format
- Alerts can be messages or emails sent to sysadmin
- Actions can be taken based upon packet type
- Snort can send output to text and databaes
- Works with MySQL, Oracle and others
- Data can be stored for trend analysis
Host File Integrity with Tripwire
- Host-baed IDS and file-integrity monitor
- Works by identifying changes to key system files
- Scans selected files and folders at regular intervals for changes
- Changes to monitored files result in alerts
- Alerts in the form of email to sysadmin
- Logs for only single system, but logs from multiple systems can be centerally managed
- Easy to use and configure
- Is not CPU intensive
- Configured from command line
- Configuration files stored in /etcx/tripwire
- Tripwire configuration file is twcfg
- Policy configurtion file is twpol
- Enable initail configuration of tripwire, then replaced by encrypted files
- Configured usung twadmin and tripwire commands
- Common files and directories to confirue for monitoring include:
- /root/, /boot, /etdc, and /usr/sbin
- hosts.allow and host.deny
- /etc/password and shadow password files
- /etc/fstab and inittab
- Initial run should baeline system
- Re-baseline system after planned patches and upgrades
- Monitor for unplanned or unauthorized changes to files
I’m a DevOps/SRE/DevSecOps/Cloud Expert passionate about sharing knowledge and experiences. I have worked at Cotocus. I share tech blog at DevOps School, travel stories at Holiday Landmark, stock market tips at Stocks Mantra, health and fitness guidance at My Medic Plus, product reviews at TrueReviewNow , and SEO strategies at Wizbrand.
Do you want to learn Quantum Computing?
Please find my social handles as below;
Rajesh Kumar Personal Website
Rajesh Kumar at YOUTUBE
Rajesh Kumar at INSTAGRAM
Rajesh Kumar at X
Rajesh Kumar at FACEBOOK
Rajesh Kumar at LINKEDIN
Rajesh Kumar at WIZBRAND
Find Trusted Cardiac Hospitals
Compare heart hospitals by city and services — all in one place.
Explore Hospitals