
The following are the best data security tools in 2023:
- Data loss prevention (DLP) software helps organizations to identify, classify, and protect sensitive data. It can be used to prevent data from being leaked or stolen, both internally and externally. Some popular DLP solutions include:
- Symantec Data Loss Prevention
- IBM Security Guardium
- McAfee Data Loss Prevention
- Proofpoint Data Loss Prevention
- Cisco Secure Web Appliance
- Encryption software scrambles data so that it cannot be read without the correct key. This can be used to protect data at rest, in transit, and in use. Some popular encryption solutions include:
- BitLocker
- VeraCrypt
- OpenSSL
- GnuPG
- PGP
- Firewalls control incoming and outgoing network traffic, and can be used to block unauthorized access to sensitive data. Some popular firewall solutions include:
- Cisco ASA
- Palo Alto Networks PA-Series
- Check Point Firewall-1
- Fortinet FortiGate
- SonicWall TZ Series
- Intrusion detection systems (IDS) and intrusion prevention systems (IPS)** monitor network traffic for malicious activity. IDS systems only alert administrators to suspicious activity, while IPS systems can also take action to block attacks. Some popular IDS/IPS solutions include:
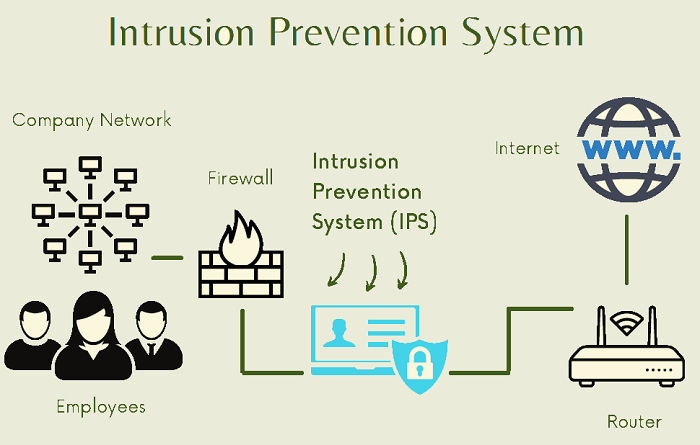
- Snort
- Suricata
- Cisco Next-Generation IPS
- Palo Alto Networks WildFire
- Fortinet FortiGuard
- Vulnerability scanners scan systems for security vulnerabilities. This can help organizations to identify and fix security problems before they can be exploited by attackers. Some popular vulnerability scanners include:
- Nessus
- Nmap
- OpenVAS
- QualysGuard
- Tenable.sc
- Data backup and recovery solutions protect data from loss or corruption. This is important for ensuring that data can be restored in the event of a cyberattack or other disaster. Some popular data backup and recovery solutions include:

- Veeam Backup & Replication
- Acronis True Image
- Backblaze B2
- Carbonite
- CrashPlan
These are just a few of the many data security tools available. The best tool for a particular organization will depend on its specific needs and requirements.
In addition to these tools, organizations should also implement security best practices, such as:
- Strong passwords and multi-factor authentication
- Regular security updates
- Employee training on security awareness
- Physical security measures to protect data centers and other sensitive areas
By implementing a comprehensive data security strategy, organizations can help to protect their data from unauthorized access, use, disclosure, disruption, modification, or destruction.

👤 About the Author
Ashwani is passionate about DevOps, DevSecOps, SRE, MLOps, and AiOps, with a strong drive to simplify and scale modern IT operations. Through continuous learning and sharing, Ashwani helps organizations and engineers adopt best practices for automation, security, reliability, and AI-driven operations.
🌐 Connect & Follow:
- Website: WizBrand.com
- Facebook: facebook.com/DevOpsSchool
- X (Twitter): x.com/DevOpsSchools
- LinkedIn: linkedin.com/company/devopsschool
- YouTube: youtube.com/@TheDevOpsSchool
- Instagram: instagram.com/devopsschool
- Quora: devopsschool.quora.com
- Email– contact@devopsschool.com
Find Trusted Cardiac Hospitals
Compare heart hospitals by city and services — all in one place.
Explore Hospitals