What is Hashicorp Boundary?
Hashicorp Boundary was introduced by Hashicorp company as Simple and secure remote access.
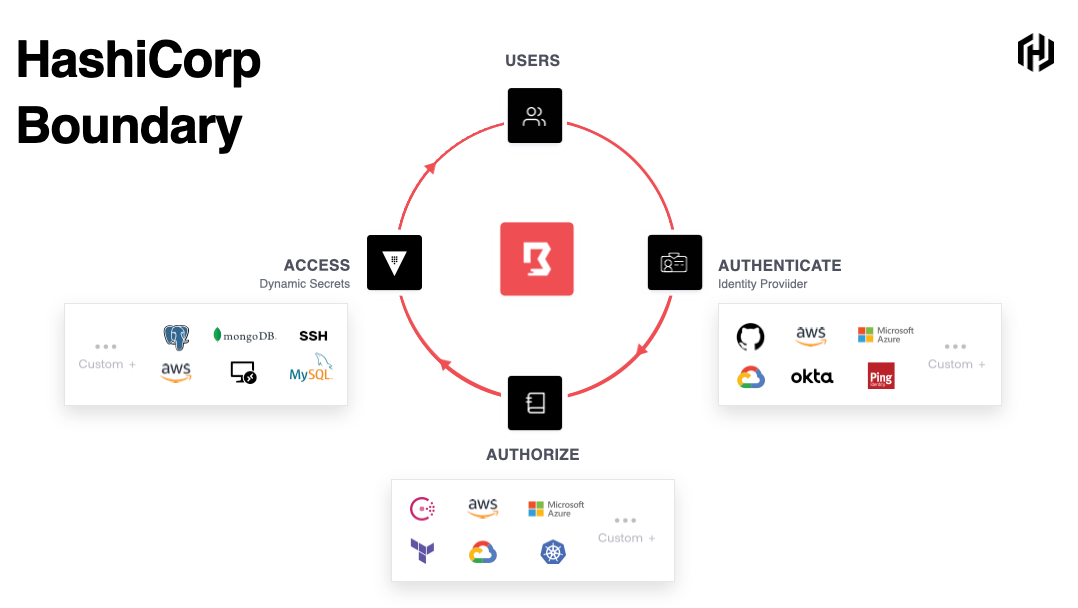
HashiCorp Boundary is a secure remote access solution that provides an easy way to allow access to hosts and critical systems with fine-grained authorizations based on trusted identities.
Boundary is designed to grant access to critical systems using the principle of least privilege, solving challenges organizations had to face when users need to securely access applications and machines.
Traditional products that grant access to systems are cumbersome, painful to maintain, or are black boxes lacking extensible APIs.
Boundary allows authenticated and authorized users to access secure systems in private networks without granting access to the larger network where those systems reside.
What is the use of Hashicorp Boundary?
- Identity-based access for zero trust security – Configure identity-based access conrols for your infrastructure, wherever it resides.
- Compliance without over-head – Provide session visibility that enables team to stay compliant.
- Fully integrated secrets management – Just in time credentials from vault for SSO to critical infrastructure targets.
List of Hashicorp Boundary Certification
There is no official certification of Hashicorp boundary right now.
Hashicorp Boundary Certification path
As mentioned above there is no official certification from Hashicorp but still you can become Boundary certified professional by getting certified from DevOpsSchool and ScmGalaxy institute.
Best Hashicorp Boundary Certification Tutorials
https://learn.hashicorp.com/collections/boundary/getting-started
Best Hashicorp Boundary Certification Video Tutorials
I’m a DevOps/SRE/DevSecOps/Cloud Expert passionate about sharing knowledge and experiences. I have worked at Cotocus. I share tech blog at DevOps School, travel stories at Holiday Landmark, stock market tips at Stocks Mantra, health and fitness guidance at My Medic Plus, product reviews at TrueReviewNow , and SEO strategies at Wizbrand.
Do you want to learn Quantum Computing?
Please find my social handles as below;
Rajesh Kumar Personal Website
Rajesh Kumar at YOUTUBE
Rajesh Kumar at INSTAGRAM
Rajesh Kumar at X
Rajesh Kumar at FACEBOOK
Rajesh Kumar at LINKEDIN
Rajesh Kumar at WIZBRAND
Find Trusted Cardiac Hospitals
Compare heart hospitals by city and services — all in one place.
Explore Hospitals