Credit – https://zawyatech.com/data-masking-tools/
Are you worried about the security of your sensitive data? Data masking can help you keep your data secure from unauthorized access. In this article, we will provide you a list of some of the best data masking tools available in the market.
What is Data Masking?
Data masking is a technique used to protect sensitive data by obscuring or masking it so that it can be used for testing, development, or training purposes without revealing its true identity. This method involves replacing the original data with a fictitious data set that appears real but is not. Data masking can be done using various techniques such as encryption, tokenization, and obfuscation.
List of Data Masking Tools
Here is a list of some of the best data masking tools available in the market:
1. Delphix

Delphix is a powerful data masking tool that allows organizations to mask sensitive data without disturbing the application functionality. This tool uses a combination of advanced techniques such as tokenization, encryption, and data substitution to mask the data. Delphix provides a user-friendly interface that enables users to create and manage masking rules easily.
2. Informatica
Informatica is a popular data masking tool that provides a wide range of masking techniques such as encryption, tokenization, and data substitution. This tool supports various data sources such as databases, files, and applications. Informatica offers a flexible and scalable platform that can be customized according to the user’s requirements.
3. IBM InfoSphere Optim
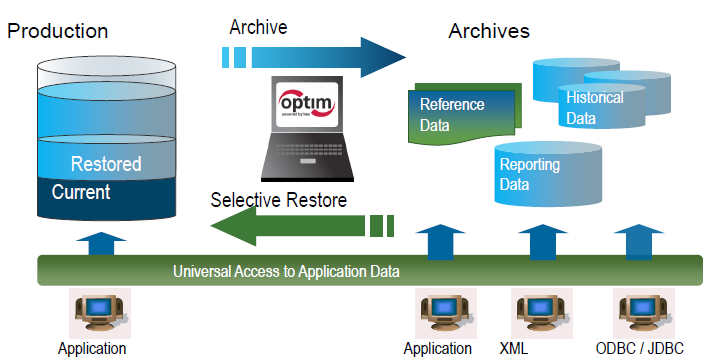
IBM InfoSphere Optim is a comprehensive data masking tool that provides advanced masking techniques such as encryption, tokenization, and data substitution. This tool supports various data sources such as databases, files, and applications. IBM InfoSphere Optim offers a user-friendly interface that enables users to create and manage masking rules easily.
4. Oracle Data Masking and Subsetting
Oracle Data Masking and Subsetting is a powerful data masking tool that provides various masking techniques such as encryption, tokenization, and data substitution. This tool supports various data sources such as databases, files, and applications. Oracle Data Masking and Subsetting offers a flexible and scalable platform that can be customized according to the user’s requirements.
5. HushHush

HushHush is a simple yet powerful data masking tool that provides various masking techniques such as encryption and tokenization. This tool supports various data sources such as databases, files, and applications. HushHush offers a user-friendly interface that enables users to create and manage masking rules easily.
Conclusion
Data masking is an essential technique that helps organizations protect their sensitive data from unauthorized access. In this article, we have provided you with a list of some of the best data masking tools available in the market. These tools provide advanced masking techniques such as encryption, tokenization, and data substitution and support various data sources such as databases, files, and applications. Choose the right data masking tool based on your requirements and keep your data secure.

👤 About the Author
Ashwani is passionate about DevOps, DevSecOps, SRE, MLOps, and AiOps, with a strong drive to simplify and scale modern IT operations. Through continuous learning and sharing, Ashwani helps organizations and engineers adopt best practices for automation, security, reliability, and AI-driven operations.
🌐 Connect & Follow:
- Website: WizBrand.com
- Facebook: facebook.com/DevOpsSchool
- X (Twitter): x.com/DevOpsSchools
- LinkedIn: linkedin.com/company/devopsschool
- YouTube: youtube.com/@TheDevOpsSchool
- Instagram: instagram.com/devopsschool
- Quora: devopsschool.quora.com
- Email– contact@devopsschool.com
Find Trusted Cardiac Hospitals
Compare heart hospitals by city and services — all in one place.
Explore Hospitals