What is Identity and Access Management?
Identity and Access Management (IAM) refers to the security discipline that enables the right individuals to access the right resources at the right times for the right reasons. IAM encompasses the management of digital identities, authentication, authorization, and access control to systems, applications, and data. The goal of IAM is to ensure that only authorized individuals have access to critical resources, while preventing unauthorized access. This is achieved through the implementation of policies, procedures, and technologies that govern the identification, authentication, authorization, and accountability of users and the management of their access rights.
Top Identity & Access Management Tools
Some of the top Identity and Access Management (IAM) tools are:
- Okta
- Microsoft Azure Active Directory
- Auth0
- OneLogin
- AWS Identity and Access Management (IAM)
- Google Cloud Identity
- IBM Security Access Manager
- Ping Identity
- RSA SecurID Access
- CA Single Sign-On.
Identity & Access Management (IAM) Best Practices
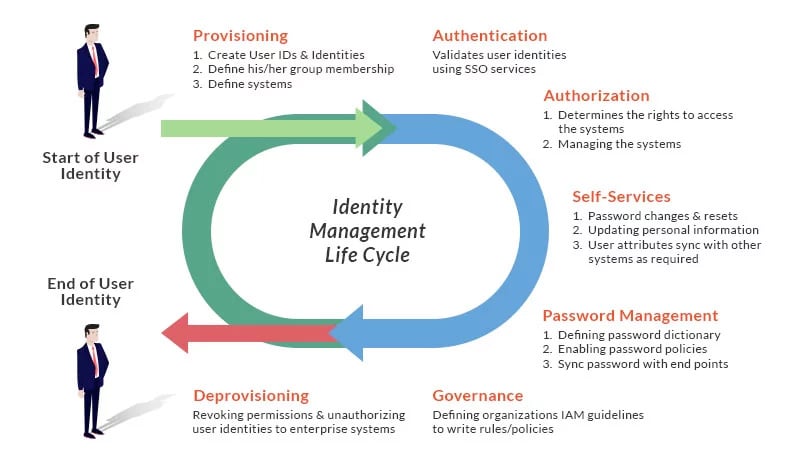
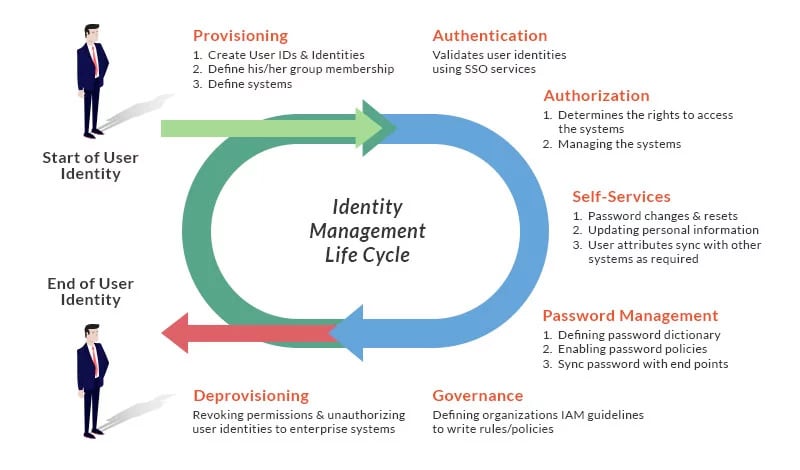
Identity & Access Management (IAM) LifeCycle
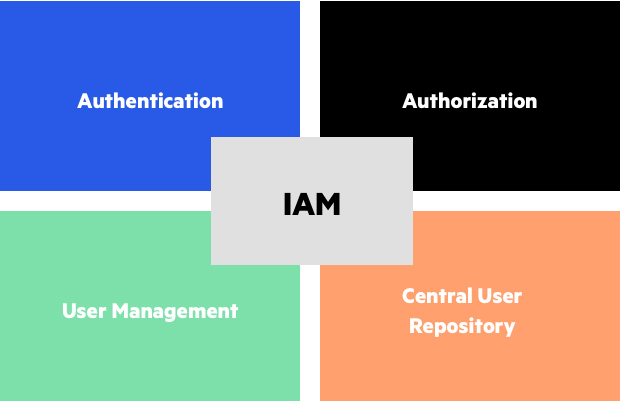
Identity & Access Management (IAM) Component

I’m a DevOps/SRE/DevSecOps/Cloud Expert passionate about sharing knowledge and experiences. I have worked at Cotocus. I share tech blog at DevOps School, travel stories at Holiday Landmark, stock market tips at Stocks Mantra, health and fitness guidance at My Medic Plus, product reviews at TrueReviewNow , and SEO strategies at Wizbrand.
Do you want to learn Quantum Computing?
Please find my social handles as below;
Rajesh Kumar Personal Website
Rajesh Kumar at YOUTUBE
Rajesh Kumar at INSTAGRAM
Rajesh Kumar at X
Rajesh Kumar at FACEBOOK
Rajesh Kumar at LINKEDIN
Rajesh Kumar at WIZBRAND
Find Trusted Cardiac Hospitals
Compare heart hospitals by city and services — all in one place.
Explore Hospitals